| Developer: | Gatelink Ltd (8) | ||
| Price: | * Free | ||
| Rankings: | 5 (1) | ||
| Reviews: | 5 (1) Write a Review | ||
| Lists: | 0 + 0 | ||
| Points: | 0 + 3 ¡ | ||
| Points + 1 | |||
Description

The application allows the following actions:
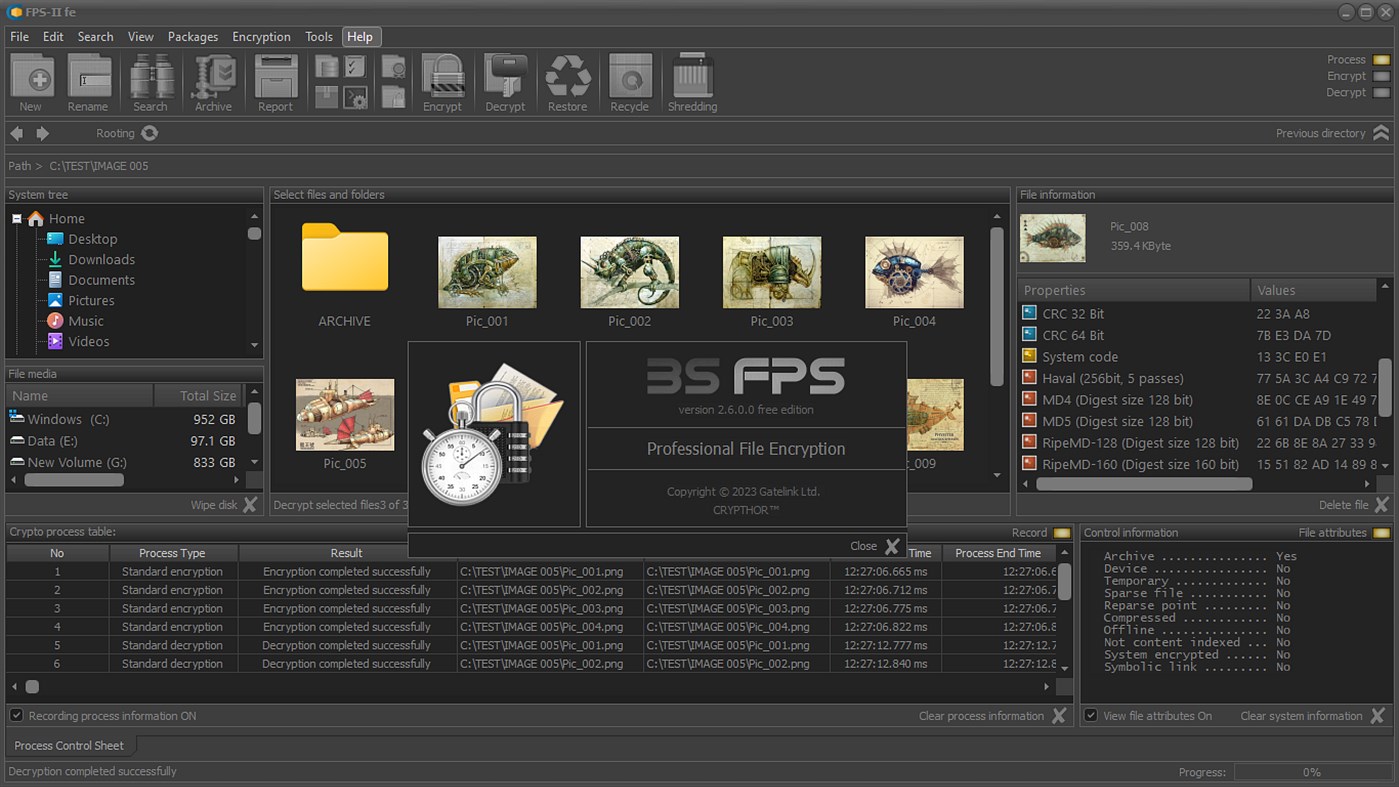
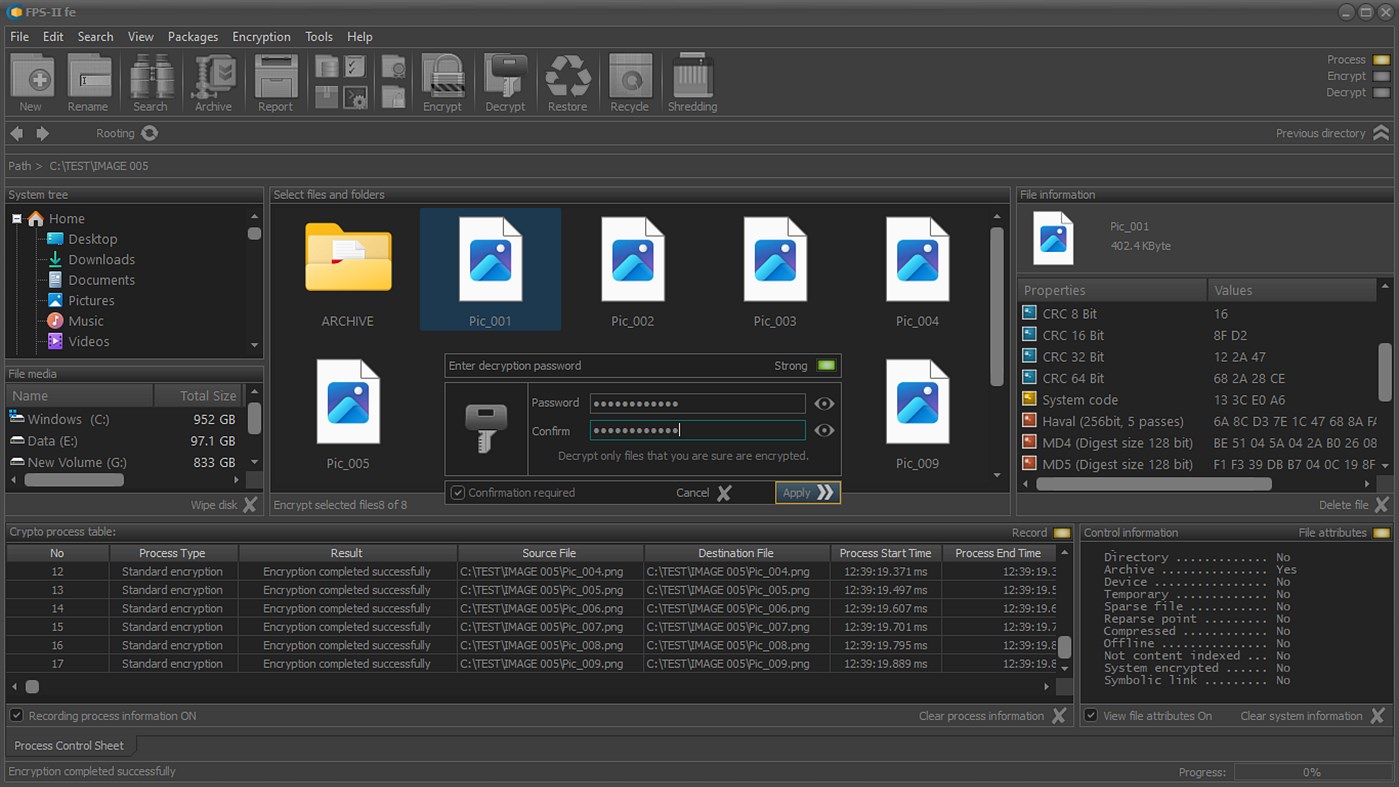
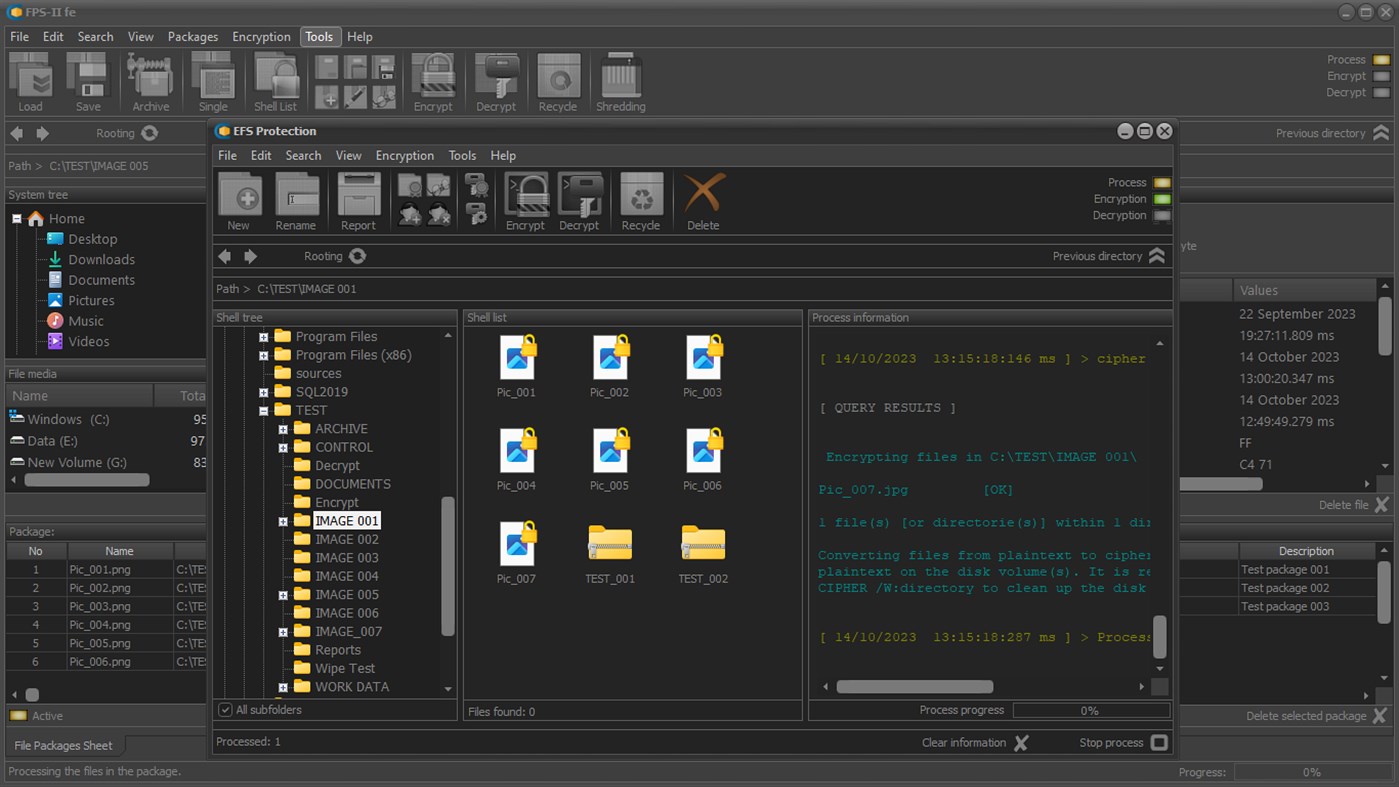
• Encrypt or decrypt selected files and folders;
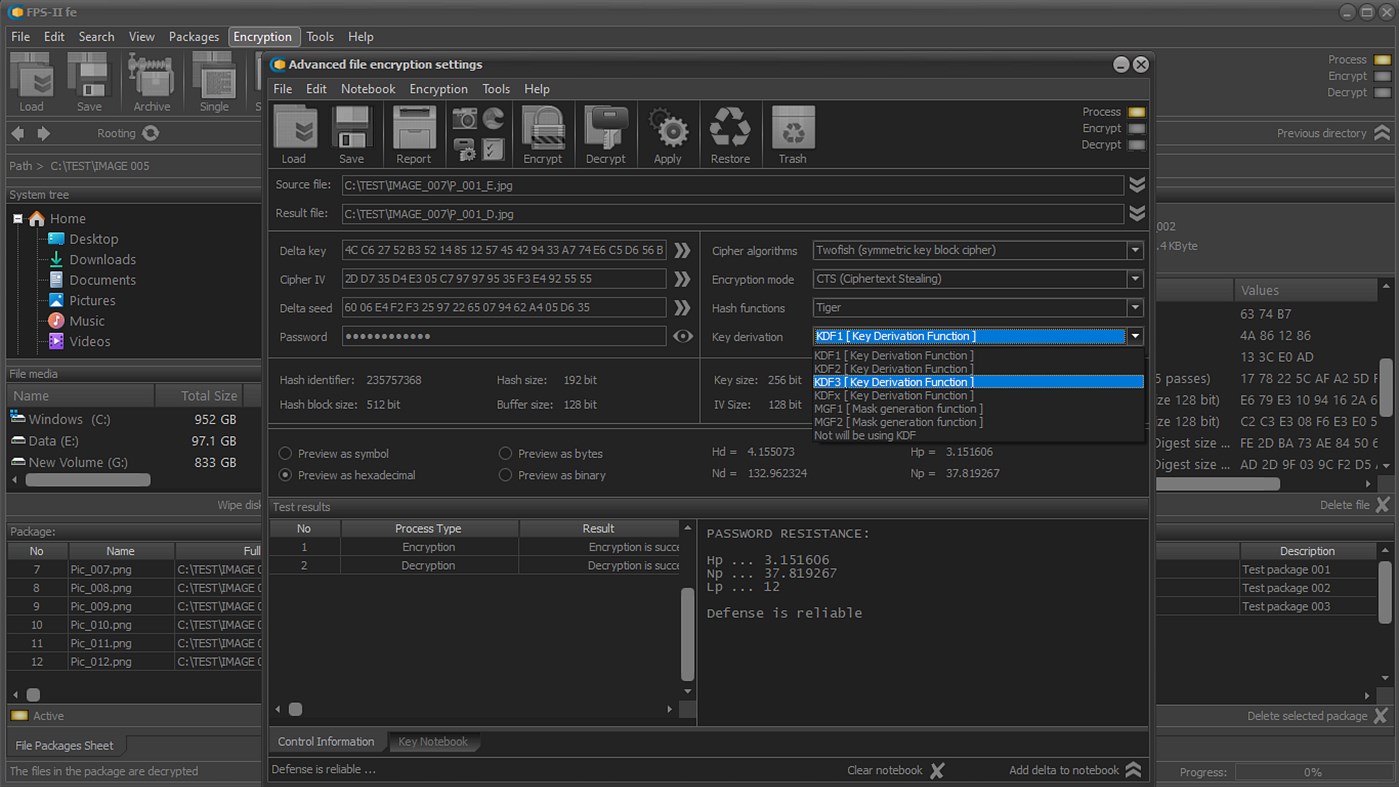
• Management of the cryptographic primitives used;
• Storing the used primitives in secure electronic notebooks;
• Management of delta cryptographic primitives (implicit security primitives, ISP);
• Formation of session secret keys based on randomly selected delta primitives (CDP encryption);
• Recording the critical information in implicit security form.
• Management of digital certificates (generation, export, signing, etc.);
• Secure electronic notebooks for storing digital certificates and secret keys;
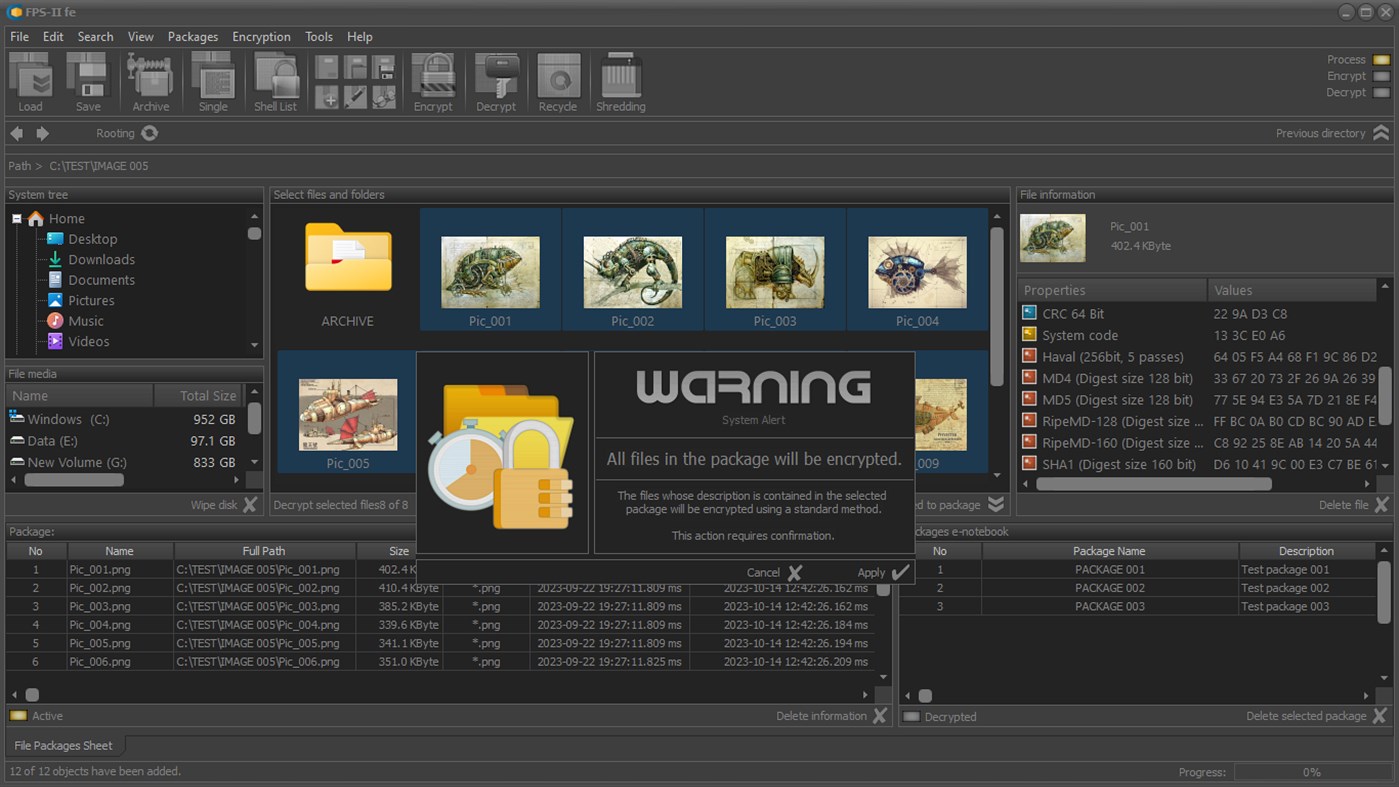
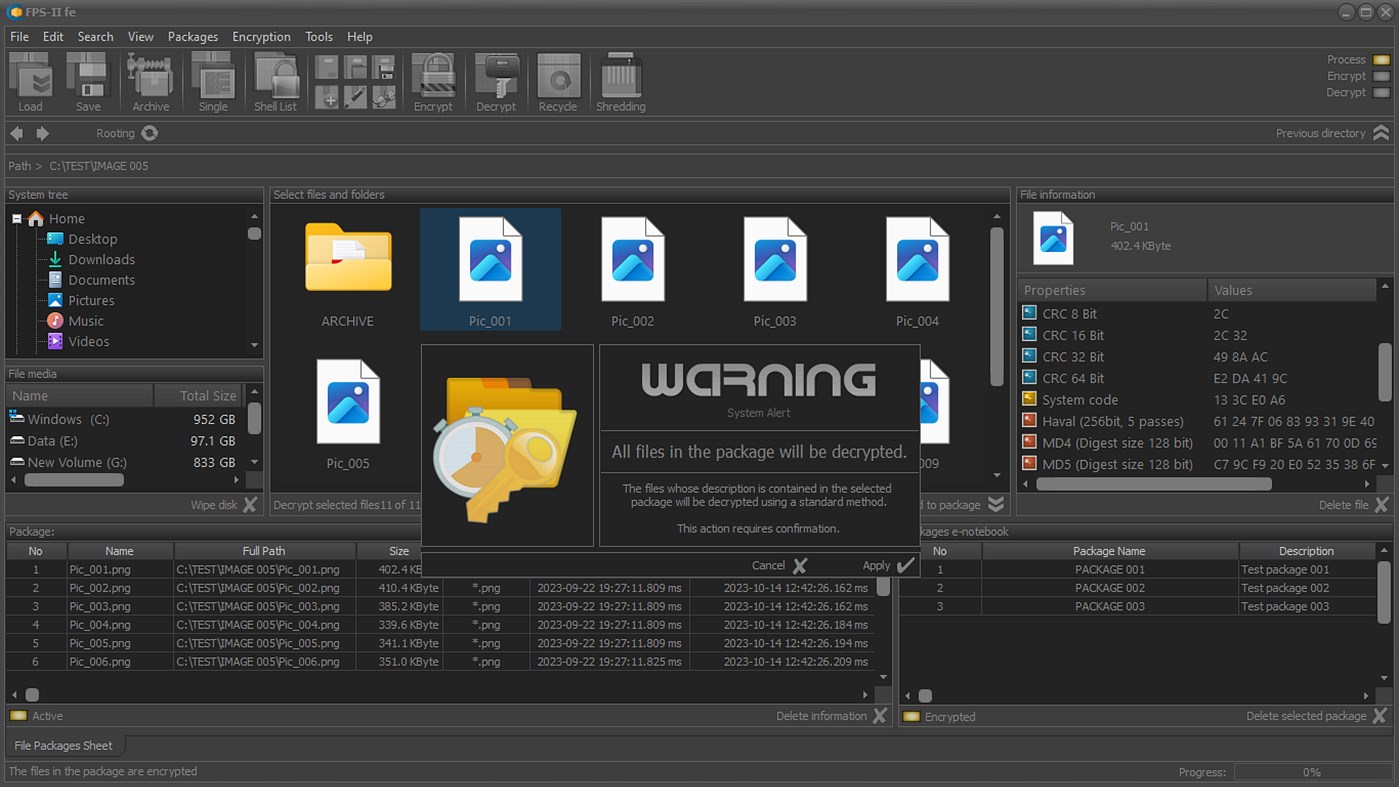
• Management of cryptographic processes for file packages;
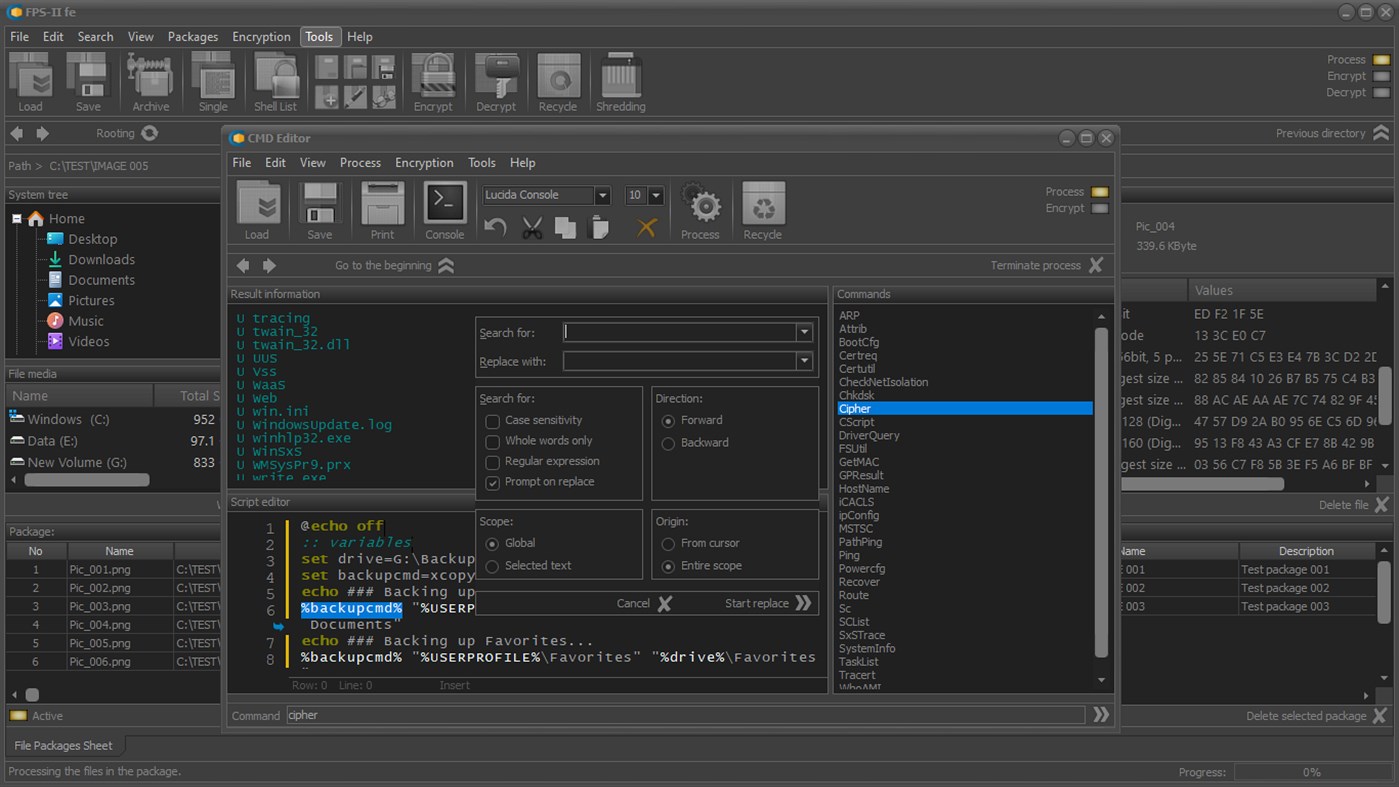
• Design and implementation of meta scenarios for the protection of digital data;
• Real-time processes control;
• Automatic formation of official reports;
• Management of the processes related to the destruction of critical information, etc.
FIELD OF APPLICATION
Protecting large arrays of files located on different media is a complex and difficult process to perform.
Procedures related to the storage, editing, transfer, and destruction of files are of utmost importance to ensure compliance with security protocols during the exploitation cycle.
Statistics show that most unauthorized access attempts aim at the critical information in specific files, including the authentication certificates used.
FPS enables the maximum reduction of risks by using a set of highly effective professional solutions to protect both specific groups of files and any information located on data storage devices
The application uses some of the most effective standard encryption algorithms used by government organizations and corporate structures.
The module for the formation of service reports makes the application an indispensable tool when building cyber security systems that meet the requirements of ISO - ISO/IEC 27001 and ISO - ISO/IEC 27002.
The development process used both standard algorithms described in NIST SP 800-88 and NIST SP 800-90A, which include Hash DRBG (based on a hash function), HMAC DRBG (based on HMAC), and CTR DRBG (based on block ciphers in counter mode), as well as some specific solutions used in the technology BS 1443, BS 7122, etc.
TECHNOLOGICAL SOLUTIONS
The correct choice of algorithms and software technologies for digital data encryption is a guarantee of the high efficiency and reliability of the application.
The application uses a set of standard and modified algorithms for encrypting mechanisms.
The following standard algorithms are used in the base versions:
STANDARD ENCRYPTION ALGORITHMS
(basic technologies)
• Blowfish
• CAST-128 [ CAST-5 ]
• CAST-256 [ CAST-6 ]
• Data Encryption Standard [ DES ]
• Triple DES [ 3DES ]
• Information Concealment Engine [ ICE ]
• Thin-ICE [Information Concealment Engine]
• Information Concealment Engine 2 [ ICE-2 ]
• IDEA [ PGP ]
• MARS
• MISTY1 [ MISTY-1 ]
• Ron’s Code or Rivest’s Cipher 2 [ RC-2 ]
• Ron’s Code or Rivest’s Cipher 4 [ RC-4 ]
• Ron’s Code or Rivest’s Cipher 5 [ RC-5 ]
• Ron’s Code or Rivest’s Cipher 6 [ RC-6 ]
• Advanced Encryption Standard [ AES, Rijndael ]
• Serpent
• Tiny Encryption Algorithm [ TEA ]
• Twofish
AFFORDABLE HASH FUNCTIONS
(basic technologies)
• Haval [ 256 Bit, 5 passes ]
• Message Digest 4 [ MD-4 ]
• Message Digest 5 [ MD-5 ]
• RIPEMD-128
• RIPEMD-160
• Secure Hash Algorithm 1 [ SHA-1 ]
• SHA-256 [ SHA-2 family ]
• SHA-384 [ SHA-2 family ]
• SHA-512 [ SHA-2 family ]
• Tiger
STANDARD ENCRYPTION MODES
(basic technologies)
• CBC (Cipher Block Chaining)
• CFB (Cipher Feedback)
• CFB8 (Cipher Feedback 8)
• CTR (Counter Mode )
• OFB (Output Feedback Mode)
The available hybrid solutions for the non-special purpose versions are as follows:
SPECIAL ALGORITHMS
(hybrid technology)
• BS Standard Protection Mode (SPM) - Crypto-mechanisms are generated by using specialized control panels. Each of these crypto mechanisms uses a set of cryptographic primitives that can be session-based or stored in highly secure digital containers.
BS Package Protection Mode (PPM) - The crypto mechanisms used are common to each of the files, information about which is contained in the file package. In case of need, individual elements of the crypto mechanisms can be hardware dependent or be tied to the use of control strings.
• BS Hybrid Protection Mode (HPM) - In this case, each of the files in the package is encrypted using a session crypto mechanism, which is formed based on the information in the electronic notebook and the specialized areas in the control strings. In addition, individual elements of the meta-information about the files and folders stored in the package are used.
ACCORDANCE WITH ACCEPTED STANDARDS:
• ISO 10116: Information Processing - Modes of Operation for an n-bit block cipher algorithm.
• ISO 9797: Data cryptographic techniques - Data integrity mechanism using a cryptographic check function employing a block cipher algorithm.
• ISO 9798-2: Information technology - Security techniques - Entity authentication mechanisms - Part 2: Entity authentication using symmetric techniques.
• ISO 10118-2: Information technology - Security techniques - Hash-functions - Part 2: Hash-functions using an n-bit block cipher algorithm.
• ISO 11770-2: Information technology - Security techniques - Key management - Part 2: Key management mechanisms using symmetric techniques.
• FIPS 140 - Federal Information Processing Standard (FIPS) 140-2, Security Requirements for Cryptographic Modules, May 25, 2001
(including Change Notices as of December 3, 2002).
• FIPS 180 - Federal Information Processing Standard (FIPS) 180-4, Secure Hash Standard (SHS), March 2012.
• FIPS 197 - Federal Information Processing Standard (FIPS) 197, Advanced Encryption Standard (AES), November 2001.
• FIPS 198 - Federal Information Processing Standard (FIPS) 198-1, The Keyed-Hash Message Authentication Code (HMAC), July 2008.
• SP 800-38D - National Institute of Standards and Technology Special Publication (SP) 800-38D, Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC, November 2007.
• SP 800-57 - NIST Special Publication (SP) 800-57 Part 1 Revision 3, Recommendation for Key Management - Part 1: General, July 2012.
• SP 800-90B - NIST Special Publication (SP) 800-90B (Draft), Recommendation for the Entropy Sources Used for Random Bit Generation, August 2012.
• SP 800-90C - NIST Special Publication (SP) 800-90C (Draft), Recommendation for Random Bit Generator (RBG) Constructions, August 2012.
• SP 800-107 - NIST Special Publication (SP) 800-107 Revision 1, Recommendation for Applications Using Approved Hash Algorithms, August 2012 etc.
What's new
- Version: PC
- Updated:
Price
-
*In-App Purchases - Today: Free
- Minimum: Free
- Maximum: Free
Track prices
Developer
- Gatelink Ltd
- Platforms: Windows Apps (8)
- Lists: 0 + 0
- Points: 2 + 5 ¡
- Rankings: 5 (3)
- Reviews: 5 (2)
- Discounts: 0
- Videos: 0
- RSS: Subscribe
Points
Not found ☹️
Rankings
-
- 35 Semes
- 5
Lists
Not found ☹️
Reviews
-
- 35 Semes
- 5
An amazing product with great features.
The mail client was something I had never seen.
In the paid version, it can also encrypt messages.
Very good interface.
easy to break down and a very convenient product.
It is a pity that there is no editor that was in the old version, but as far as I understand it will be offered as a separate solution.
Additional Information
Contacts
- Website:
https://fps.g-92.com
You may also like
-
- File Protect System-SE
- Windows Apps: Security By: Gatelink Ltd
- $179.99
- Lists: 0 + 0 Rankings: 5 (1) Reviews: 5 (1)
- Points: 2 + 0 Version: PC File Protect System (version FPS-II se) is a specialized, hybrid application for managing the life cycle of critical information that is stored on local or server data devices. The ...
-
- File Locker X - Password Protect Files
- Windows Apps: Security By: IO Stream Co., Ltd
- $4.99
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 11 Version: PC Password-protect files and folders to secure your sensitive data and decrypt your data back easily. Encrypt and decrypt multiple files or folders at once. There's no limit to how many ...
-
- File Privacy
- Windows Apps: Security By: Needed Special Tools
- Free
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 3 + 2 Version: PC 3DES is one of the most prominent forms of encryption and has a symmetric-key block cipher algorithm. File Privacy uses Triple DES (3DES or TDES). You encrypt your files using the key ...
-
- File Secure
- Windows Apps: Security By: Rapid Technologies Pakistan
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 3 Version: PC Encrypt your files with password. This application allows you to encrypt your data with password to avoid publicising.
-
- Paranoia File Encryption & Text Encryption PRO
- Windows Apps: Security By: Paranoia Works
- $3.49
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 2 Version: PC The application comprises two modules: File Encryptor: This module allows you to securely encrypt your private and confidential files or entire folders. You can accomplish the ...
-
- Folder & File Lock
- Windows Apps: Security By: MedhaChaitanya
- * Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 1,448 Version: PC The folder and file protection software that you are waiting for is now here! I have completely re-worked on the app. Thank you for all the feedback and reviews for the initial ...
-
- DSE File Encryptor
- Windows Apps: Security By: Data Safety Expert
- Free
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 2 + 4 Version: PC Professional file encryptor and decryptor. This app uses the best encryption algorithms available today: AES-128, AES-192 and AES-256. Optionally, this app can sign the encrypted file ...
-
- HCrypto - File ecryption / Safe
- Windows Apps: Security By: wang h.
- $1.99
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 7 Version: PC HCrypto 2.0 is here 1. Batch encrypt files/folders 2. Monitor the folder and automatically encrypt the files in the folder 3. File Safe, safe to host your private files 4. Text ...
-
- Protecta Encryption Software
- Windows Apps: Security By: PROTECTA
- Free
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 2 Version: PC Protect your important private documents with strong AES (Rijndael), Twofish or Threefish cryptography using an intuitive easy-to-understand software interface. - Multiple files and ...
-
- Avast Antivirus Download Center
- Windows Apps: Security By: AVAST Software
- Free
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 50,957 Version: PC Protect your Windows 10 PC against viruses, ransomware, spyware, and other types of malware with Avast Free Antivirus. Used by more than 400 million people around the world, our free ...
-
- Penteract Disguised-Keyboard Detector 2
- Windows Apps: Security By: Penteract LLC
- $3.99
- Lists: 1 + 0 Rankings: 0 Reviews: 0
- Points: 2 + 4 Version: PC Protect your computer from evil USB devices. Protects your computer from "USB flash drives" which are actually malicious automatic keyboards masquerading as USB flash drives. It does ...
-
- IObit Malware Fighter
- Windows Apps: Security By: IObit (Both Talent International Limited)
- * Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 8 Version: PC Elevated permissions are required to install and run IObit Malware Fighter. IObit Malware Fighter is a powerful and comprehensive anti-malware and anti-virus program that can protect ...
-
- Acer ProShield Plus
- Windows Apps: Security By: Insyde Software Corp.
- Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 1 + 3 Version: PC Acer ProShield Plus and Acer ProShield Plus Service are built-in applications, and they're only supported on Acer devices. Acer ProShield Plus Service is a separate software suite that
-
- Safe UWP
- Windows Apps: Security By: NxeCcde24 Labs
- * Free
- Lists: 0 + 0 Rankings: 0 Reviews: 0
- Points: 0 + 8 Version: PC Keep any files hidden safe from prying eyes in Safe UWP! - The ultimate secret gallery app to hide videos, pictures, music, documents and etc. on your Windows devices. Sensitive files ...